
AI Document Management
PandaDoc AI Contract Assistant simplifies document management and review. Explore our AI assistant’s contract workflow capabilities and intelligent contract insights.
Finish your demo booking
Looks like you haven't picked a time for your personalized demo. Pick a time now.
Select date and time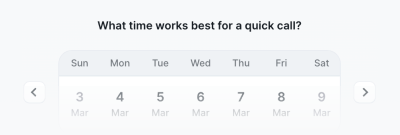
Everything you need to streamline document workflows.
No credit card required
Get personalized 1:1 demo with our product specialist.
By submitting this form, I agree that the Terms of Service and Privacy Notice will govern the use of services I receive and personal data I provide respectively.